Online sharks, also known as cybercriminals or internet predators, are individuals or groups who use the internet to commit various types of crimes and exploit others for personal gain. These crimes can range from identity theft and fraud to cyberbullying and sexual exploitation.
One of the main ways that online sharks operate is through phishing scams, where they send fake emails or create fake websites in an attempt to trick people into giving out sensitive information such as login credentials or financial information. These scams can be incredibly convincing, often mimicking the branding and design of legitimate websites or companies.
Another common tactic used by online sharks is to exploit vulnerabilities in computer systems or networks in order to gain unauthorized access or steal sensitive data. This is known as hacking, and it can be done for a variety of reasons such as stealing trade secrets, spreading malware, or disrupting critical infrastructure.
Online sharks also often use social media and other online platforms to prey on individuals, particularly children and teenagers. They may pretend to be someone else in order to gain trust and exploit that trust for their own benefit. This can include grooming behavior, where they gradually build a relationship with a child and gradually exploit their trust, leading to serious consequences such as sexual abuse.
It is important to be aware of these online threats and take steps to protect yourself and your family. This includes using strong passwords, being cautious when clicking on links or giving out personal information, and using antivirus software to protect against malware. It is also important to educate children about internet safety and to monitor their online activities to ensure that they are not being exploited by online sharks.
Overall, online sharks are a serious threat to individuals and society as a whole, and it is important to be aware of their tactics and take steps to protect ourselves and our loved ones from their predatory behavior.
Terrifying moment shark reveals protruding razor sharp teeth like monster from Alien

To receive the discount, enter JOLLY150 in the coupon code box during checkout. To build this app, the Atlantic White Shark Conservancy worked in close conjunction with the Cape Cod National Seashore and the Massachusetts Division of Marine Fisheries, and Cape Cod and South Shore towns officials. Ocearch was the organization that found Mary Lee, a 3,456-pound, 16-foot long great white shark who visited the shores of Chesapeake Bay. That way, it is easy to see how to play the game. To unsubscribe at any time text STOP to 1-855-540-0007. To receive the discount, enter JOLLY60 in the coupon code box during checkout.
Vacuum Cleaners, Steam Mops & Irons

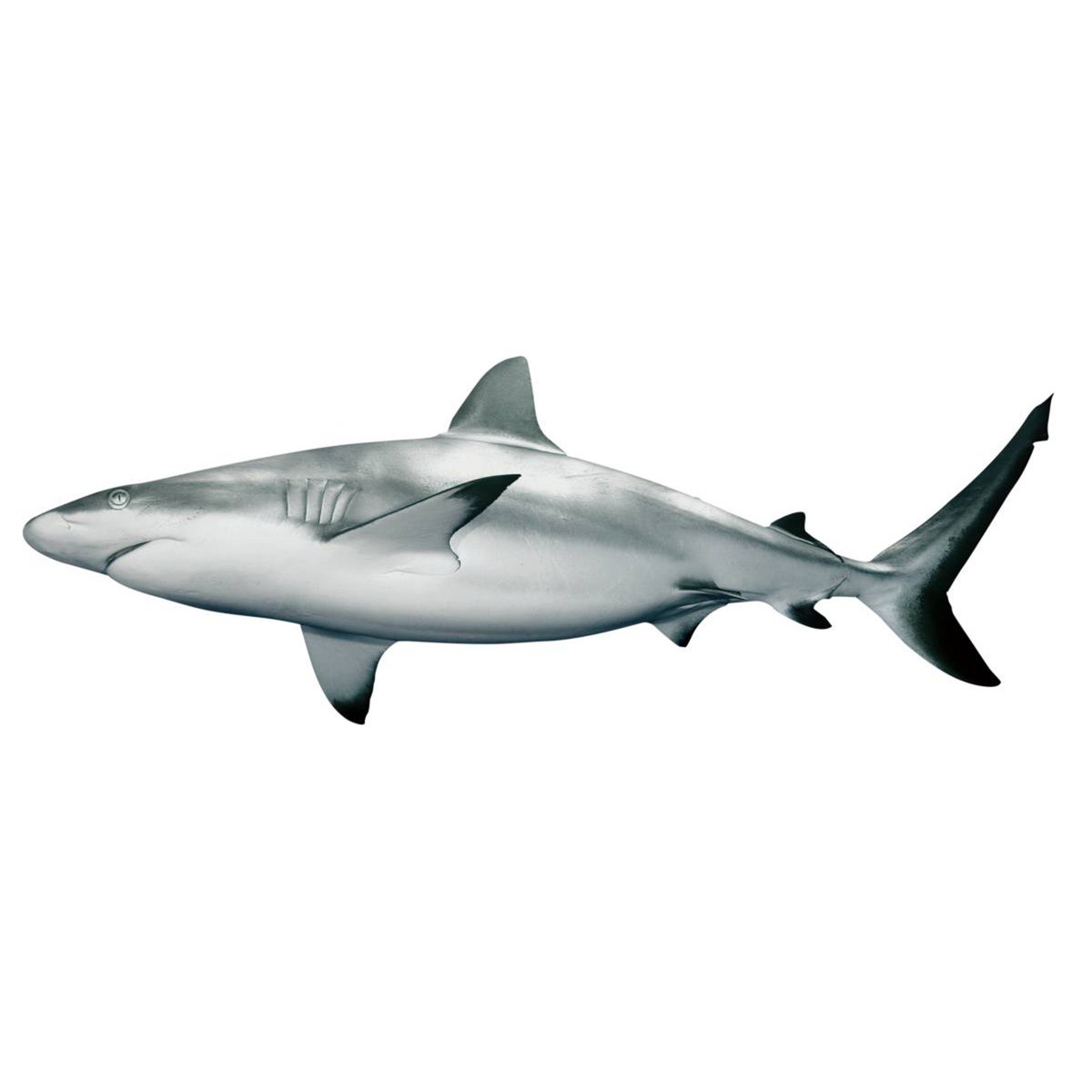
Some species shed and replace up to 30,000 teeth in a lifetime! Attack and kill swimming people, boats or even humans out of the water. Coupon code can only be used once per order. Their jagged teeth are to move quickly from within the skull, allowing it to use its entire mouth as it goes to take a bite out of its prey. You can see this data on unique tracking maps like those below, allowing you to follow sharks as they roam around the globe. There are currently around 500 different species. Avoid running out of blood or your great white shark will be the one finding death. To save 10% on all accessories, enter JOLLY10 in the coupon code box during checkout.
Shark Games
The footage was uploaded to SHARK PANIC Terrifying moment SHARK stalks prey just feet from swimmers on busy Dubai beach One person said: "It is comical how spooky and simultaneously not a concern for humans these buggers are. Some of the world's not sending data in real time. SharkNinja reserves the right to cancel or modify this offer at any time. Survive Kill, eat, and grow. Message frequency: No more than 10 messages per month. The Smart Position tag, otherwise known as the Temperature Transmitting Tag SPOT , is a special tag in that it displays the location of a shark every time it comes above the surface of the water for more than 90 seconds. Orders cannot be shipped to PO boxes or Hawaii, Alaska, Puerto Rico or other territories outside of the contiguous 48 states.
Hungry Shark Arena

These tiger sharks were tagged with the latest and greatest in satellite tagging technology, allowing us to see where they are at every time they break the surface of the water. Continue reading to find out more about sharks and our catalogue of games. This white shark broke the water's surface off the Georgia coast most recently. To receive the discount, enter JOLLY75 in the coupon code box during checkout. They survive on a diet of bony fish, other sharks and crustaceans. This is a high-quality shark game that you can play here in your browser. You can even sink your pointy teeth into water planes and rescue choppers to drag them down into the water! The app has 250,000 users as of today and features a wide range of reports from official channels, including several Dorsal aerial surveillance partners.
To receive the discount, enter JOLLY30 in the coupon code box during checkout. Guy Harvey Research Shark Tracking With the Guy Harvey Research tracking tool, you can track sharks of all kinds. The game is made with HTML5 to run in modern browsers. Are you ready to be cruel like this? Limit one discount per customer per transaction. Similar to the sand tiger shark, the Alien's mouth has the ability to extend its jaw to reveal a powerful set of teeth which can chew through bone and metal. Beyond the location of these sharks, the tags give us important oceanographic data, including sea surface temperature, oxygen profiles, and deeper ocean temperature. Terrorize the bays and beaches in these games and cause maximum chaos with your sleek, aquatic predator! In early May of 2017, Mary Lee visited the shores of Assateague Island and, at one point, even traveled into Chincoteague Bay.